Overview
Reveal supports integration with Azure Active Directory to fetch Employee details into Reveal Hold. This document describes the prerequisites for integrating Reveal Hold with Azure AD.
Information Required for Integration
The following details are required for configuring the Azure Active Directory connector in Reveal Hold.
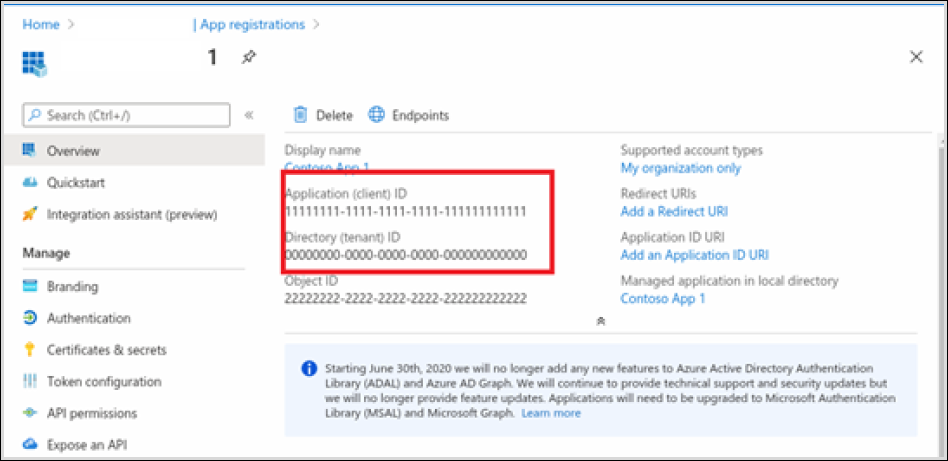
Client ID and Tenant ID of the registered application in Azure.
Client secret generated for the application.
The below sections describe the steps to be carried out to enable Azure Active Directory integration with Reveal Hold.
Register Application in Azure
Registering an application establishes a trust relationship between the app and the Microsoft identity platform. The trust is unidirectional: the app trusts the Microsoft identity platform, and not the other way around.
Follow the steps given below to create the app registration:
Sign in to the Azure portal.
If access to multiple tenants is available, from the top menu, use the Directory + subscription filter to select the tenant in which the application is to be registered.
Search for and select Azure Active Directory.
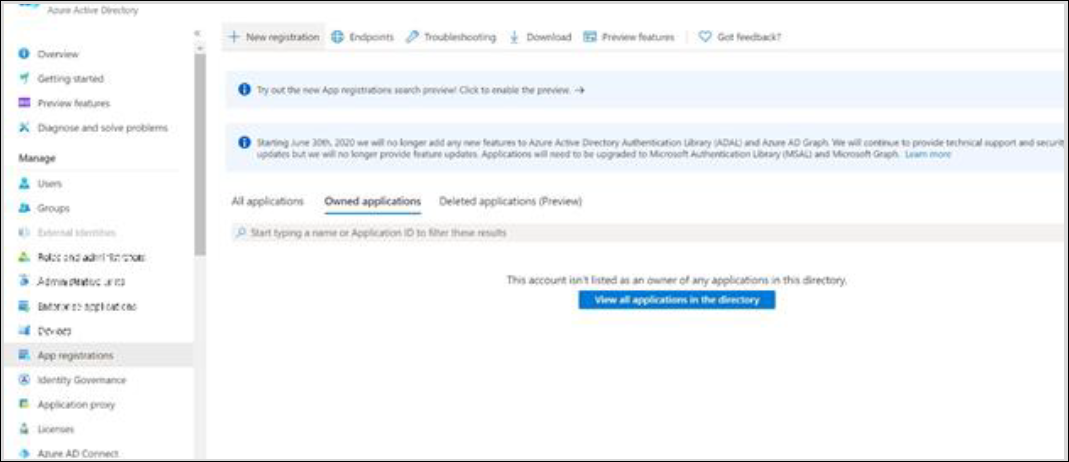
Under Manage, select App registrations > New registration.
Enter a Display Name for the application. Users of the application might see the display name when they use the app, for example, during sign-in. The display name can be changed at any time and multiple app registrations can share the same name. The app registration's automatically generated Application (client) ID, not its display name, uniquely identifies the app within the identity platform.
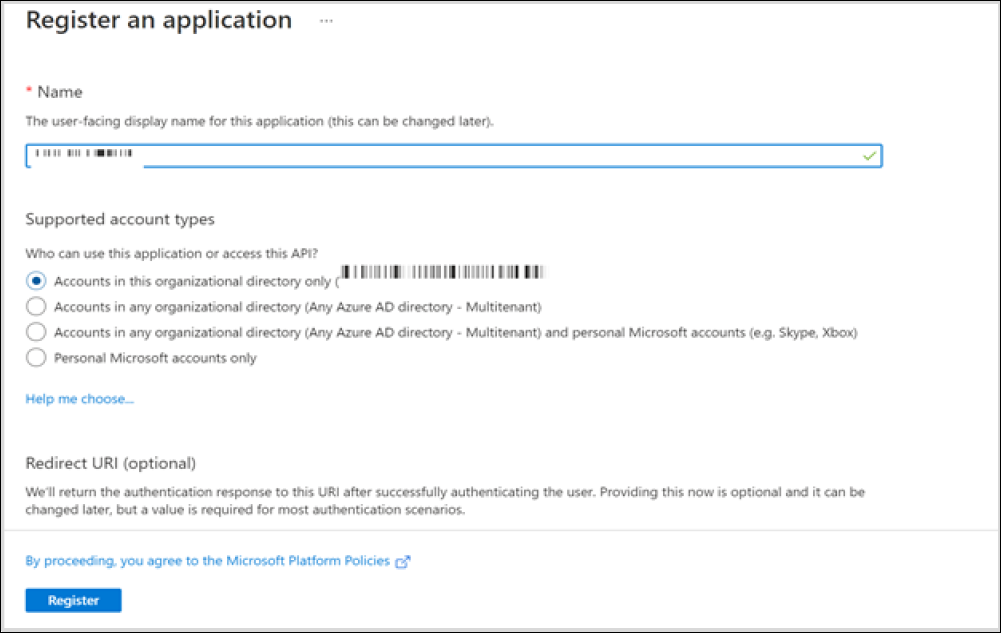
Specify Accounts in this organizational directory only can use the application. In some cases it is known as Sign-in audience.
Do not enter Redirect URI (optional). The following section describes how to configure a redirect URI.
Select Register to complete the initial app registration.
Add a Redirect URI
A redirect URI is the location where the Microsoft identity platform redirects a user's client and sends security tokens after authentication. In a production web application, for example, the redirect URI is often a public endpoint where the app is running.
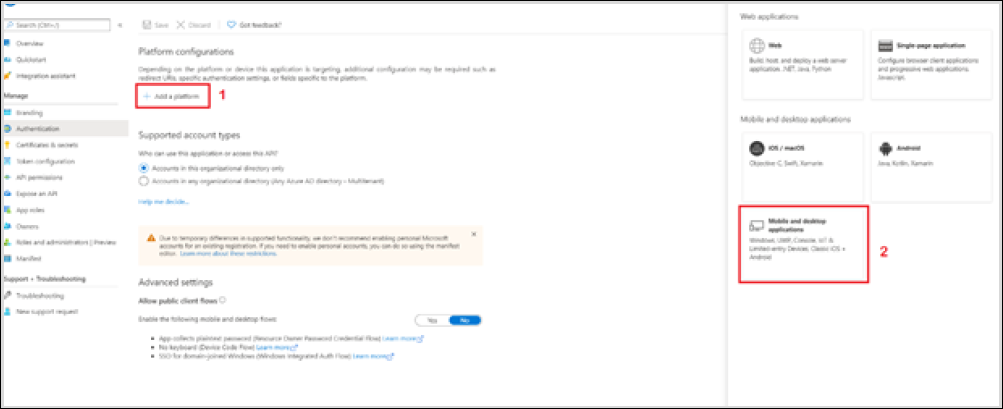
Mobile and Desktop Applications
Select one of the suggested redirect URIs. For desktop applications using embedded browsers, https://login.microsoftonline.com/common/oauth2/nativeclient needs to be checked.
Select Configure to complete the platform configuration.
Add a Client Secret
The client secret is also known as an application password. It is a string value the app can use in place of a certificate to identify itself. The client secret is the easier of the two credential types to use.
To add a Client Secret, first select the application from App registrations in the Azure portal. Then follow the steps given below.
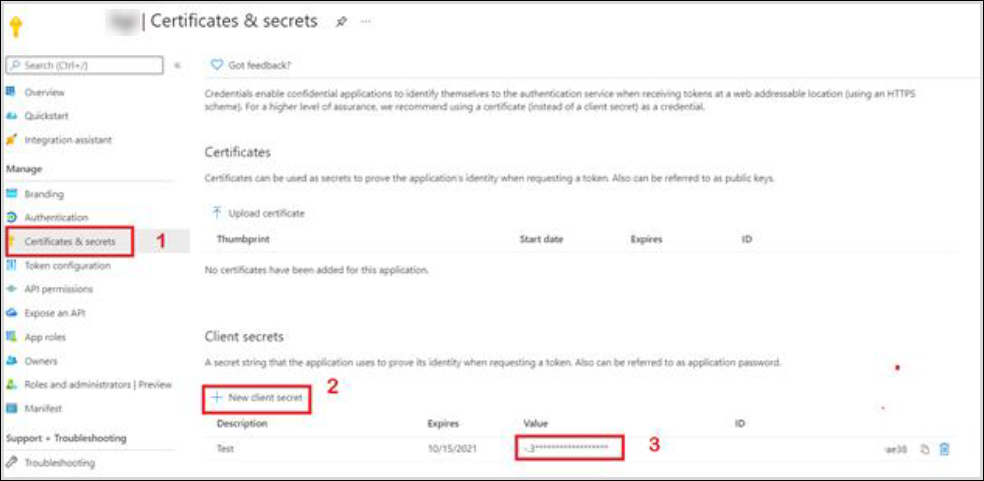
Select Certificates & secrets.
Select New client secret.
Add a Description and an Expiry for your client secret.
Select Add.
Record the secret's value for use in the client application code.
This secret value is never displayed again after leaving this page.
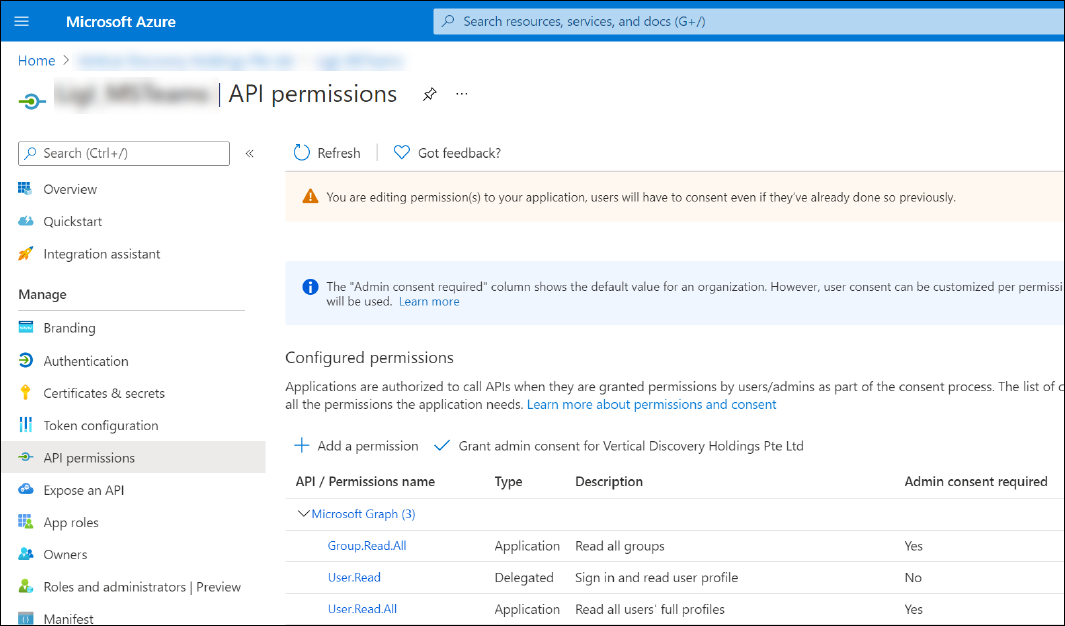
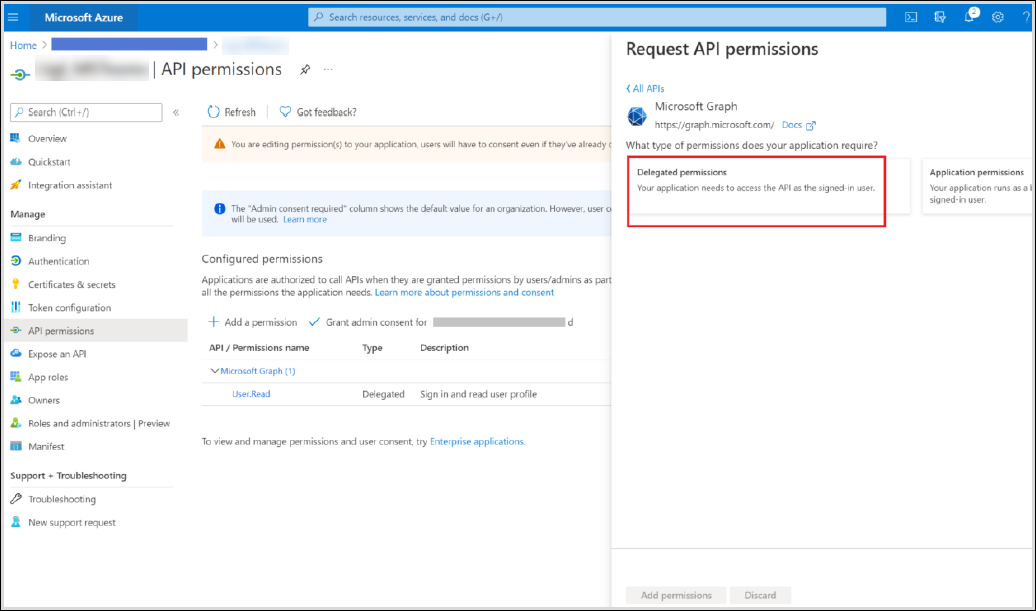
Add Permissions to Access Microsoft Graph
Configure delegated permission to Microsoft Graph to enable the client application to perform operations on behalf of the logged-in user, such as reading their email or modifying their profile. By default, users of the client app are asked, when they sign in, to consent to the delegated permissions configured for it.
To configure permissions,
Choose API permissions to view the options.
Select Add a permission > Microsoft Graph.
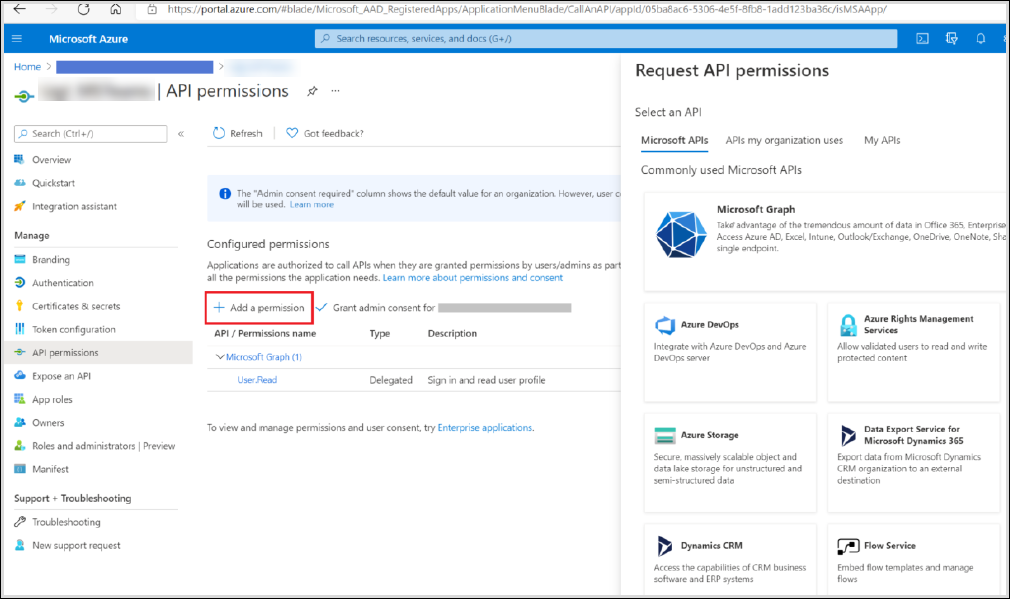
Select Delegated permissions. Microsoft Graph exposes many permissions, with the most commonly-used shown at the top of the list.
Under Select permissions, select the following permissions and navigate to Application Permissions, adjacent to Delegated permissions, to Select Application permissions listed in below table.
API / Permissions name | Type | Description | Admin consent required |
Group.Read.All | Application | Read all groups | Yes |
User.Read.All | Application | Read all users' full profiles | Yes |
User.Read | Delegated | Sign in and read user profile | No |